‣ How to Implement SPF Authentication?
‣ How to Use DKIM Authentication?
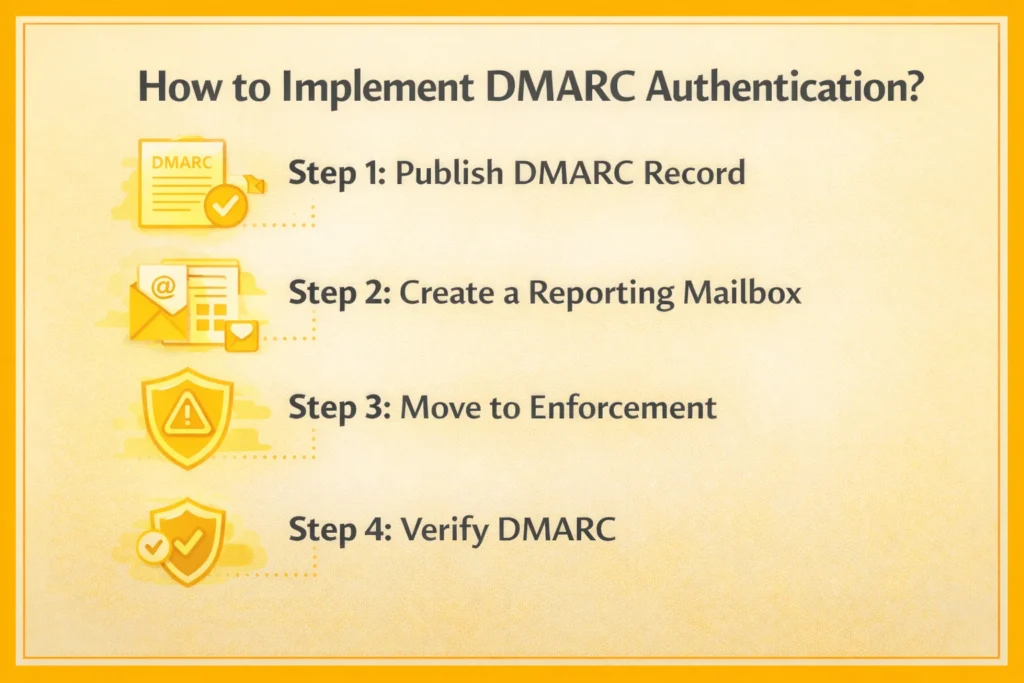
‣ How to Implement DMARC Authentication?
‣ One-Click Unsubscribe Configuration
‣ Spam Complaint Monitoring
‣ Common Implementation Errors
‣ How to Implement DKIM Authentication?
‣ Domain Alignment and Subdomain Strategy
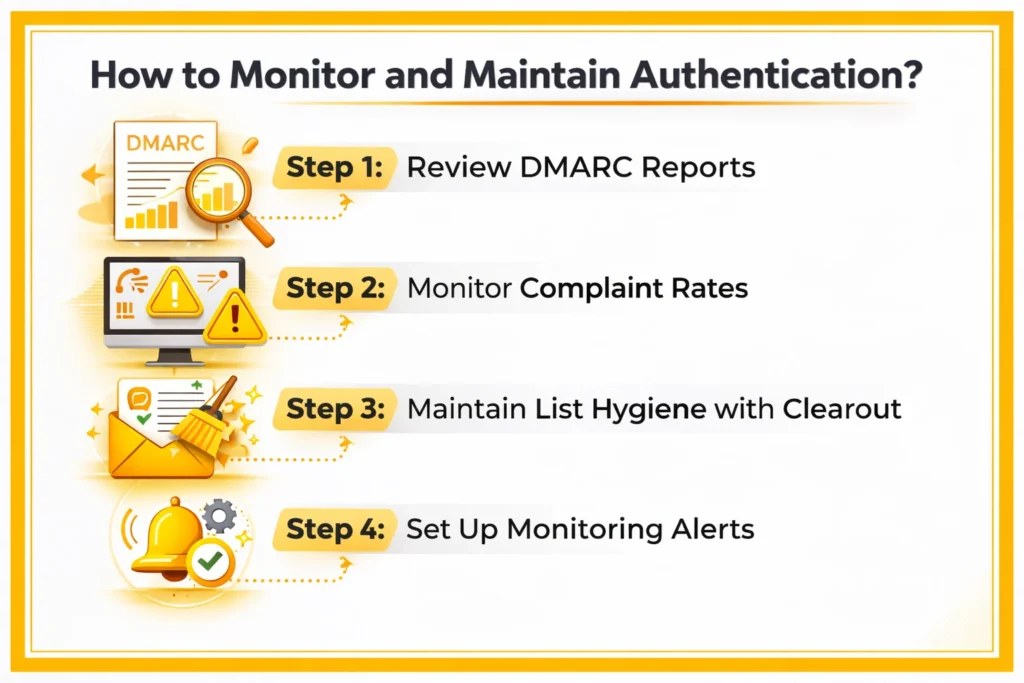
‣ How to Monitor and Maintain Authentication?
‣ How to Troubleshoot Common Authentication Issues?
‣ Your Authentication Implementation Checklist
‣ FAQs